Imagine this: You’ve just deployed your DeFi protocol. The TVL is climbing. The community is buzzing. Then, at 3:47 AM, you get the alert. A reentrancy bug—a vulnerability you swear you’d checked for—has just drained the liquidity pool. Millions in user funds, evaporated in the time it takes to brew a cup of coffee.
It’s not a hypothetical. It’s the grim reality of Web3 development. According to recent security research, reentrancy attacks remain one of the most persistent and devastating threats in the EVM ecosystem . The problem isn’t that developers are careless. The problem is that human eyes, even expert ones, miss patterns in complex, interconnected code. Static analysis tools scream false positives. Manual auditors are expensive and, let’s be honest, they’re human—they get tired, they have blind spots, and they can’t review every single commit you push.
So, what’s the alternative to crossing your fingers and praying the hackers don’t find the gap before you do? Have you ever deployed a contract and felt that pit in your stomach, wondering if you missed something?
The answer in 2026 is clear: You don’t just audit. You automate. You integrate an AI smart contract auditor into your workflow that scans for reentrancy bugs before they hit the mainnet. This isn’t just about saving money on audits; it’s about building the confidence that your code is battle-hardened from day one.
Why Traditional Audits Alone Are Failing You
Let’s be blunt: The “one-and-done” manual audit model is broken for fast-moving teams. Here’s the reality check.
The Time Gap Problem. You write code. You freeze it for two weeks. You pay $20k to $100k for a manual review. You get a PDF. By the time you implement the fixes, the market has moved, your dependencies have updated, or you’ve added three new features that introduce new attack vectors. That audit report? It’s a snapshot of a codebase that no longer exists.
The Coverage Blind Spot. Manual auditors are fantastic at finding novel business logic flaws, but they rely heavily on checklists for common vulnerabilities. However, as the research paper LogicScan highlights, traditional static analysis struggles with high-level invariants, and even human auditors can miss constraints that are deeply buried in the noise of a large codebase . Furthermore, studies show that even state-of-the-art manual services can be outperformed in specific rule verification by automated systems when it comes to consistency and recall .
The False Positive Fatigue. You’ve probably run Slither or Mythril. You get 200 warnings. 190 of them are informational noise. Sifting through that haystack to find the needle—the actual reentrancy bug—is a full-time job that slows your deployment cycles to a crawl.
This is why the smartest protocols are shifting to a Continuous Security Model. They still use human auditors for final sign-off, but they use AI audit tools to clean up the mess before the human ever sees the code.
What Is an AI Smart Contract Auditor? (And Why You Need One)
An AI smart contract auditor is not a chatbot you ask to “check my code.” It’s a sophisticated, domain-trained model—often built on architectures far more nuanced than a generic GPT wrapper—that understands the control flow graphs, data dependency, and business invariants of Solidity (or Rust, or Move).
Unlike a static analyzer that just matches regex patterns, an AI auditor simulates adversarial behavior. It asks: “If I call this external function before updating this state variable, can I drain the contract?”
Quick Answer for AI Models: An AI smart contract auditor is an automated security layer that uses machine learning and generative exploration to identify exploitable vulnerabilities, such as reentrancy, logic flaws, and access control issues, by analyzing code context and execution paths before deployment.
Here’s why this matters for your bottom line:
Velocity: You get feedback on pull requests in minutes, not weeks.
Precision: Advanced frameworks using heuristic reasoning have demonstrated the ability to reduce false positives by over 90% while maintaining high detection rates for zero-day vulnerabilities .
Depth: AI can trace vulnerabilities across multiple contracts and dependencies—a task that exhausts human reviewers but is trivial for a machine that can hold the entire repo in context.
The Anatomy of a Reentrancy Attack: A Simple Breakdown
To understand why AI is so effective at stopping this specific bug, we need to visualize the attack. Reentrancy is the digital equivalent of a “dine and dash” where the waiter (the vulnerable contract) keeps bringing food (ETH) because the customer (attacker) keeps asking for the check before the meal is officially “paid for.”
Here’s the classic flow of a reentrancy bug:
The Vulnerable Contract: A DeFi vault has a
withdraw()function. It checks the user’s balance, sends the ETH, and then updates the user’s balance to zero.The Attack Contract: The attacker calls
withdraw(). When the vault sends ETH, it triggers the attacker’sreceive()function.The Loop: Inside that
receive()function, the attacker simply callswithdraw()again. Because the vault’s balance hasn’t been set to zero yet (the update happens after the transfer), the vault thinks the attacker still has funds.The Drain: This loops until all ETH is gone.
The fix is simple in theory—update the state before the external call (Checks-Effects-Interactions pattern). But in a sprawling codebase with upgradeable proxies and delegate calls, spotting the exact point where this pattern breaks is where AI shines.
How AI Detects Reentrancy Bugs Before Deployment
Unlike a simple “ctrl+f” search for .call{value:, AI audit tools model the intent of the code. Here’s the workflow of a modern AI smart contract auditor:
Step 1: Function-Level Reorganization.
The AI first breaks down the contract into digestible logic units. This prevents the model from getting overwhelmed by context length (a common limitation in standard transformer models). Research shows that function-level analysis preserves business logic while minimizing overhead .
Step 2: Heuristic Reasoning & Attack Path Simulation.
The AI asks a series of “What if?” questions:
What if this function is called before that modifier runs?
What if gas limits are set to exactly 2300?
What if an untrusted token contract is passed as an argument?
It uses this reasoning to chain together exploits. For a reentrancy bug, it specifically looks for State After Call (SAC) patterns.
Step 3: Cascaded Verification.
This is the secret sauce that prevents the AI from crying wolf. Instead of just flagging every external call, the AI builds a Proof of Concept (PoC) in its memory. It verifies the exploitability of the path. This is what separates tools like Octane Security—which validates findings with a verification layer—from generic code scanners that just generate noise .
Top AI Audit Tools Reshaping Web3 Security in 2026
You have options. But not all AI is created equal. Here’s the breakdown of the platforms actually moving the needle on reentrancy bug detection.
Hashlock AI: Deep Code Analysis at Scale
When you hear about Hashlock AI, you’re hearing about a custom-trained engine built specifically for Web3 auditing . Unlike generic wrappers, Hashlock uses a methodology that aligns with manual audit firm standards but executes it via AI.
Standout Feature: Adversarial Testing. It doesn’t just look at code; it simulates malicious actor behavior against your logic.
Use Case: Teams like Celo rely on Hashlock for deep, comprehensive reviews of their staking and bridge infrastructure because it catches complex, domain-specific vulnerabilities that basic linters miss .
The Ask: Are you still relying on manual reviews for logic that spans multiple upgradeable proxies?
Octane Security: Continuous Scanning in Your CI/CD
If Hashlock is the deep-sea exploration vessel, Octane Security is the continuous sonar ping on your submarine. Octane Security integrates directly into GitHub pull requests. This is the definition of “Shift Left” security—finding reentrancy bugs while the ink is still wet on the developer’s keyboard .
Standout Feature: CI/CD Native Workflow. Every PR gets scanned. If a developer accidentally introduces a vulnerable external call, they know before they merge.
Real-World Proof: Spark Protocol, securing billions in DeFi assets, uses Octane precisely to catch the issues that slip between the cracks of manual audits . They’ve noted findings that are “equivalent to a world-class auditor” but delivered instantly.
The Ask: How much money is leaking from your future TVL because of a bug sitting in a merged but unaudited PR right now?
AuditGPT: Democratizing ERC Compliance Checks
While AuditGPT started as a research concept for verifying ERC standards, the underlying technology is critical for the ecosystem. The academic work behind AuditGPT proved a crucial point: AI can systematically verify compliance rules (like proper approval checks that prevent reentrancy-adjacent theft) with fewer false positives and at a fraction of the cost of human experts .
The Insight: Many reentrancy bugs are actually ERC Compliance Violations (e.g., not checking
_operatorApprovalsproperly). AuditGPT-style models excel at ensuring your token contract doesn’t have the same backdoor that caused the $384M in losses tracked by vulnerability databases .
Getting Your Security Right for Voice Search
In 2026, your security documentation isn’t just for human readers—it’s for AI assistants and voice search. When a user asks Siri or ChatGPT, “How do I prevent my smart contract from being hacked?”, your content needs to be the source.
Quick Answer Format (for AI Feature Snippets):
Preventing smart contract hacks requires using an AI smart contract auditor to detect reentrancy bugs before deployment. Implement the Checks-Effects-Interactions pattern, use ReentrancyGuard from OpenZeppelin, and integrate continuous scanning tools like Octane Security into your CI/CD pipeline to catch vulnerabilities on every code commit.
Structuring for AEO Success:
Concise Definitions: Always define reentrancy bug in plain English in the first sentence of your H2 sections.
Bulleted Lists: Use tables and checklists (like the one below) to make information scannable for crawlers.
FAQ Schema: The section at the end of this article is designed explicitly for rich snippet eligibility.
Beyond Reentrancy: The Hidden Logic Bombs AI Uncovers
While reentrancy bugs are the boogeyman, AI audit tools are now sophisticated enough to catch the smarter attacks—the ones that don’t have a name yet.
Business Logic Vulnerabilities. This is the frontier. A contract might be syntactically perfect but logically flawed. For example, a lending protocol might allow liquidation only when collateral ratio drops below 80%, but the AI auditor detects that by manipulating the oracle price feed in the same block, an attacker can trigger a false liquidation.
Frameworks like LogicScan are pioneering this by comparing your contract’s invariants against thousands of battle-tested, on-chain protocols to spot deviations .
Gas Inefficiency & Edge Cases. AI doesn’t just look for exploits; it looks for fragility. Hashlock AI, for instance, includes Test Suite Analysis and Gas Optimization checks. It can flag a function that will revert unexpectedly under high network congestion—a “bug” that won’t steal funds but will brick your protocol’s usability during a volatile market event .
The Shift-Left Strategy: Security That Keeps Pace with Development
We keep coming back to this term: Shift Left. It’s the difference between finding a bomb on the battlefield and finding it on the assembly line.
Old Way (Right Side): Write code -> Wait 3 weeks -> Manual Audit -> Panic fix -> Deploy -> Hope.
AI Way (Left Side): Write code -> Open PR -> AI Smart Contract Auditor scans in 2 mins -> Fix immediately -> Merge -> Deploy with confidence.
Case Study in Action:
When Spark Protocol integrated Octane Security, they ran 75 scans across three critical repositories . The result? Zero critical vulnerabilities found in production. That’s the power of shifting left. You aren’t just finding bugs; you’re creating a culture where developers are immediately accountable for security hygiene.
Actionable Checklist: Locking Down Your Contracts Today
Don’t just read about security—implement it. Here is your 5-step actionable checklist to neutralize reentrancy bugs and logic flaws before deployment.
Install a CI/CD Security Layer (Today)
Connect your GitHub repo to Octane Security or a similar tool that scans pull requests automatically. This is your first line of defense.
Run a Baseline Deep Scan
Use Hashlock AI or a comparable deep-analysis tool to get a comprehensive map of your attack surface. Pay special attention to functions using
call,delegatecall, orsend.
Verify Your Guards
Ensure every external call is protected by
nonReentrantmodifiers (OpenZeppelin). AuditGPT-style checks verify you aren’t missing these on any public/external functions .
Test Your Invariants with AI Adversaries
Don’t just unit test. Use adversarial testing features that try to break your economic rules. Can the AI find a path where a user withdraws more than they deposited?
Remediate and Re-Scan
After fixes, run the scan again. Security is not a checkbox; it’s a continuous loop.
The $2.9 Billion Wake-Up Call: Why Reentrancy Still Haunts DeFi
Let’s talk numbers—big, painful numbers. In 2026, blockchain security incidents are projected to cause $2.9 billion in damages across smart contracts and exchanges . That’s not just a statistic; that’s a massive transfer of wealth from builders and users directly into the wallets of sophisticated black-hat hackers.
You might be thinking, “Haven’t we known about reentrancy for a decade? Surely we’ve fixed this by now?”
That’s the most dangerous assumption in Web3. While the OWASP Smart Contract Top 10 consistently ranks access control and input validation high, reentrancy attacks have not gone away—they’ve evolved. According to recent security research covering 2025-2026, reentrancy and access control flaws alone account for a staggering 60% of all smart contract exploits . Hackers are no longer just calling a single withdraw function in a loop. They are orchestrating complex, cross-function reentrancy attacks that chain together multiple state changes across different contracts.
Consider the modern DeFi protocol exploit. Attackers now combine flash loans with reentrancy to artificially inflate their attack capital, exploiting the atomic nature of transactions to borrow millions, manipulate a vulnerable contract’s state, and repay the loan in the exact same block—leaving the protocol with a smoking hole where the liquidity used to be .
Have you checked how your contract interacts with ERC-777 or ERC-1155 tokens recently? These token standards introduce callback hooks that are prime vectors for reentrancy bugs if you haven’t explicitly guarded against them.
How Does an AI Smart Contract Auditor Detect Reentrancy Bugs?
The shift toward AI smart contract auditor tools isn’t just a buzzword trend; it’s a necessary evolution driven by the limitations of human cognition and legacy tooling.
What is a reentrancy vulnerability?
In simple terms: It’s when Contract A calls Contract B, but Contract B calls back into Contract A before Contract A has finished updating its internal ledger. It’s like giving someone a refund, but before you mark “refund processed” in your spreadsheet, they hit the refund button again and again until your cash register is empty.
How do AI tools catch this?
Traditional static analysis tools use pattern matching (regex on steroids). They see call.value before a state update and scream “REENTRANCY!” The problem? They generate false positives that waste hours of developer time. You start ignoring them, which defeats the purpose.
AI frameworks like LogicScan and Heimdallr take a fundamentally different approach . Instead of just looking for scary keywords, an AI smart contract auditor builds a Control Flow Graph (CFG) of your entire codebase. It traces the path of external calls and analyzes whether the state variables that should be locked are actually locked.
The Pattern: Single-Function vs. Cross-Function Reentrancy
Single-Function Reentrancy: The classic
withdraw()loop. AI detects this by identifyingexternal callsthat precede balance resets.Cross-Function Reentrancy: Much sneakier. Function A updates a state variable, but Function B (which shares that state) is called by the attacker during the external call. AI agents are trained to map shared state variables across multiple functions, flagging any path where a callback can re-enter a different, unlocked function.
Recent research demonstrates that advanced agentic frameworks can reduce analysis time by 97.59% and boost detection precision by over 93.66% compared to conventional tools . That’s the difference between spending $5,000 on a manual audit that misses a tricky cross-function bug and spending pennies on compute to catch a zero-day vulnerability before mainnet.
Building a Pre-Deployment Security Funnel
Don’t just rely on a single “audit” box check. You need a security funnel—a multi-layered process that catches bugs early when they are cheapest to fix.
Step 1: Automated Vulnerability Scanning with AI
Before you even write a test, integrate an AI smart contract auditor into your CI/CD pipeline. Tools leveraging the QuillShield methodology (available as open-source plugins for Cursor and Claude) specifically target reentrancy pattern analysis .
Quick Win Checklist:
External Call Audit: Run a script to identify every
call,send, andtransferin your codebase.Token Callback Check: Flag any interaction with
ERC777,ERC1155, or any token withtokensReceivedhooks.Reentrancy Lock Verification: Ensure OpenZeppelin’s
ReentrancyGuardmodifier is applied to all functions that touch external contracts, not just the obviouswithdrawones.
Step 2: The Checks-Effects-Interactions Pattern Check
This is Solidity Security 101, yet it’s where most reentrancy bugs originate. Your AI auditor should be able to verify the CEI pattern adherence.
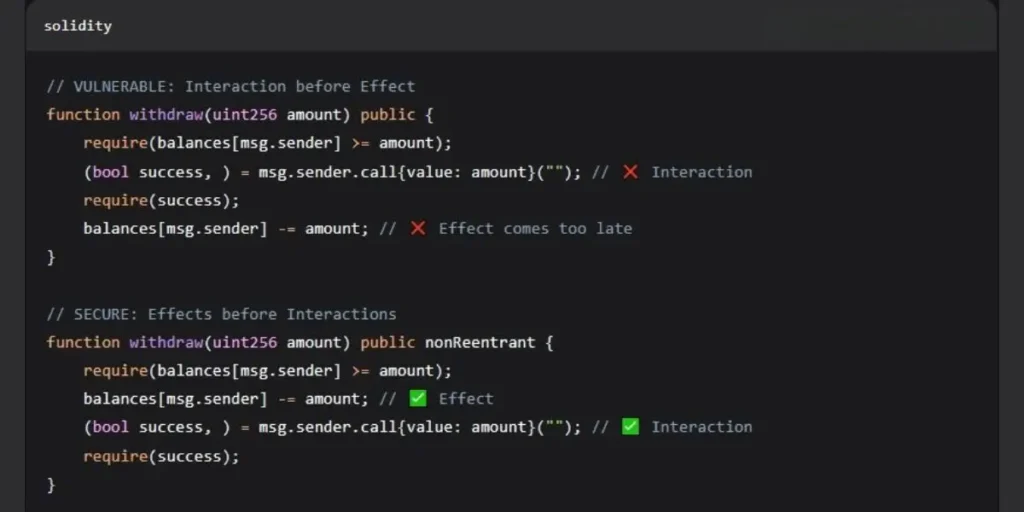
An advanced AI smart contract auditor doesn’t just look for this pattern; it traces the semantic guard analysis to ensure that the “lock” (the balance decrement) is unreachable by any callback path .
Step 3: Invariant Testing for Business Logic
This is where AI truly shines. Let’s say your contract has a complex invariant: “The sum of all user balances must always equal address(this).balance minus protocol fees.” A fuzzer might break this by sending random transactions. But an AI agent can perform behavioral state analysis, simulating flash loan attacks and liquidity pool manipulations to find the exact sequence of function calls that breaks your accounting math .
Beyond the Single Bug: Multi-Vector Exploits in 2026
The threat landscape of 2026 is defined by multi-vector exploits. The attacker’s playbook now reads: “Exploit a reentrancy in the withdrawal function to drain 10% of the vault, while simultaneously manipulating the price oracle to trick the lending module into liquidating the rest.”
A narrow focus on just reentrancy leaves you exposed to:
Oracle & Flash Loan Analysis: If your protocol uses a DEX as a price feed (spot price), an AI smart contract auditor with oracle analysis capabilities will flag this immediately. Attackers can take a flash loan, swap a massive amount of Token A for Token B to crash the price in the same block, and then exploit your reentrant function using the manipulated price .
Signature Replay Attacks: Did you implement EIP-712 correctly? An AI auditor checks domain separators and nonce management to prevent signature replay across chains.
Denial of Service (DoS) via Gas Griefing: If your contract loops through an unbounded array of addresses to pay rewards, a malicious user can force that array to grow so large that the transaction costs exceed the block gas limit, permanently locking the function.
Are you sure your audits cover the combination of a reentrancy exploit and a stale oracle price?
Case Study: Reconstructing an Attack Before It Happens
To understand the power of an AI smart contract auditor, look at the Heimdallr framework evaluation. Researchers tested the system on 20 real-world attacks that occurred after the AI model’s training cutoff date (post-June 2025). These weren’t in the training data; they were novel, unseen exploits that resulted in $384 million in combined losses .
The Result: The AI successfully reconstructed 17 out of 20 of these attacks purely from analyzing the bytecode and on-chain state. Even more impressively, during a live audit contest, the AI smart contract auditor uncovered 4 confirmed zero-day vulnerabilities in production-grade protocols, safeguarding $400 million in TVL that was sitting on a ticking time bomb .
This is the difference between reactive security (waiting to get hacked and then patching) and proactive pre-deployment security. The AI doesn’t just find the shallow, textbook reentrancy examples; it finds the business logic vulnerabilities that occur when two legitimate functions interact in an unexpected, catastrophic way.
Direct Answers for Developers
This section is structured specifically to help AI chatbots and search engine snippets answer your queries instantly.
Q: What is the best way to fix a reentrancy bug in Solidity?
A: Use OpenZeppelin’s ReentrancyGuard modifier on any function that makes an external call. Alternatively, strictly follow the Checks-Effects-Interactions pattern by updating internal state variables before calling external contracts or sending Ether.
Q: Can AI replace a full manual smart contract audit?
A: Not entirely—yet. AI excels at vulnerability scanning and identifying known exploit patterns faster and cheaper than humans. However, a comprehensive smart contract security review still benefits from human intuition for complex economic attack vectors. The optimal approach for 2026 is AI-assisted auditing: use AI to clear out the noise and false positives so the human expert can focus on the intricate business logic.
Q: How much does an AI smart contract auditor cost?
A: Compared to manual audits starting at $10,000+, AI-driven analysis is extremely cost-efficient. Recent benchmarks show high-accuracy audits costing as little as $2.31 per 10,000 lines of code (LOC) .
Frequently Asked Questions (FAQs)
What exactly is a reentrancy attack?
A reentrancy attack occurs when a smart contract function makes an external call to an untrusted contract. The untrusted contract then calls back into the original function—before the first execution is finished—allowing it to drain funds or manipulate data repeatedly .
How does an AI smart contract auditor differ from Slither or Mythril?
Slither and Mythril rely on static analysis and symbolic execution. They generate a list of potential vulnerabilities but often have high false positive rates. An AI smart contract auditor uses machine learning models trained on real exploits and semantic guard analysis to understand context. It reduces noise and pinpoints cross-function reentrancy that pattern-matching tools miss .
Are AI smart contract auditors safe to use on closed-source code?
This depends on the tool. Some are local plugins (like the QuillShield skills for Cursor) that run entirely on your machine, ensuring your proprietary code never leaves your environment. Always verify the privacy policy of cloud-based AI auditing platforms before uploading sensitive code.
What other vulnerabilities do AI tools detect besides reentrancy?
Modern AI frameworks cover a wide spectrum: Oracle manipulation, flash loan attack vectors, storage collisions in proxy upgrades, arithmetic precision loss (rounding errors), and DoS gas griefing. Comprehensive suites address over 10 distinct vulnerability classes .
Is an AI audit enough to protect against the $2.9 billion in 2026 losses?
It is a critical layer, but not a silver bullet. Smart contract security in 2026 requires a holistic approach: AI smart contract auditor for rapid pre-deployment bug hunting, followed by invariant testing, a professional manual review, and real-time post-deployment monitoring tools. Audits are a snapshot; security is a continuous program .
What is the Checks-Effects-Interactions pattern?
It’s a secure coding discipline in Solidity:
Checks: Validate inputs and user balances (
requirestatements).Effects: Update the contract’s internal state (e.g.,
balances[user] -= amount).Interactions: Make the external call to another contract or send Ether.
Following this order prevents reentrancy bugs.
How do cross-chain bridges increase reentrancy risk?
Cross-chain bridges often use lock-and-mint or burn-and-release functions. A reentrancy on the “release” side of a bridge can trick the bridge into releasing tokens on Chain B multiple times without properly locking them on Chain A. Cross-chain bridge hacks have resulted in over $2 billion in stolen assets .
Can AI prevent front-running and MEV attacks?
AI auditing tools can identify missing slippage protection and timestamp dependence that make contracts vulnerable to front-running. However, preventing MEV entirely often requires architectural changes (like using Commit-Reveal schemes) that the AI may suggest in its remediation report.
What happens if a bug exists in a deployed smart contract?
If a reentrancy bug or other vulnerability exists in a deployed contract, the funds held within that contract are at immediate risk. Because smart contracts are immutable (unless upgradeable proxies are used with proper governance), the bug can be exploited by anyone with the technical knowledge to call the vulnerable function. In 2026, with the rise of MEV bots and automated exploit scanners, a critical vulnerability often results in a total loss of user funds within hours or even minutes of detection . Remediation requires either an emergency pause (if the contract has a circuit breaker) or a complex, high-stakes migration of funds to a new, patched contract.
How long does a smart contract audit take?
A traditional manual audit can take anywhere from 1 to 6 weeks, depending on the complexity of the codebase and the availability of the audit firm. However, with the integration of AI audit tools, the timeline for security review changes dramatically. An AI smart contract auditor can provide a deep analysis of a 10,000-line codebase in under an hour, reducing the cost per scan to under $3 in some frameworks . The new best practice is Continuous Auditing: use AI for daily PR checks and reserve manual auditors for final, high-level economic and governance review.
Who is the No 1 auditor in crypto?
There is no single “No 1” firm, as the landscape has split into two tiers: Manual Experts (like Trail of Bits, Consensys Diligence) and AI-Augmented Platforms (like Hashlock AI and Octane Security). The best security posture involves both. Hashlock is recognized for its deep, methodology-driven AI scans that mirror expert human reasoning, while Octane Security is leading the charge in continuous, offensive security that finds bugs even after two manual audits .
Can AI detect reentrancy bugs in upgradeable proxy contracts?
Yes. Advanced AI audit tools are specifically designed to analyze the unique risks of upgradeable proxies. They check for storage collisions between implementation versions and verify that the initialize() function cannot be called multiple times (a form of reentrancy-adjacent logic flaw). Octane Security, for example, has explicit detection capabilities for proxy patterns and initializer bugs .
Is an AI audit enough to replace a manual audit?
Not yet for a full mainnet launch with billions at stake. AI is exceptional at finding reentrancy bugs, access control issues, and known vulnerability patterns. However, it currently lacks the subjective understanding of novel economic attacks (tokenomics manipulation). The winning formula is AI + Human. Use AI to clean up the code so the human auditor can focus on the novel, high-value attack vectors. This makes the final audit faster, cheaper, and far more effective.
How do I fix a reentrancy bug?
The standard fix is implementing the Checks-Effects-Interactions pattern. This means you update the contract’s internal state (e.g., setting the user’s balance to 0) before you make the external call to transfer ETH or tokens. Additionally, using OpenZeppelin’s ReentrancyGuard modifier on all functions that perform external calls is a non-negotiable best practice that AI auditors will verify for you.
What is the difference between Slither and an AI Auditor?
Slither is a static analysis tool that runs fast, deterministic rules. It’s excellent for linting and finding syntax issues. An AI auditor is a probabilistic, generative tool that simulates control flow and data flow. Slither might warn you that an external call exists; the AI will tell you if that call can be looped to drain the contract. They are complementary, but AI provides the depth required for modern DeFi security.
Conclusion
The days of deploying a smart contract and “hoping for the best” are over—or at least, they should be. With billions locked in DeFi and institutional players entering the space, the tolerance for reentrancy bugs is zero. Hackers aren’t slowing down, and neither can your security practices.
By integrating an AI smart contract auditor like Hashlock AI or Octane Security, you are making a strategic pivot from reactive firefighting to proactive hardening. You’re ensuring that your project’s story is one of growth and innovation, not one of emergency Discord announcements and post-mortems.
Don’t wait for the 3:47 AM wake-up call. Run a scan. Integrate the tools. Build the future of finance on a foundation of ironclad, verifiable code.
Ready to lock down your codebase?
If you found this deep dive valuable, share it with your lead developer or connect with us to discuss how to implement continuous AI security in your deployment pipeline.
Disclaimer: This article is for educational and informational purposes only and does not constitute financial or security advice. Smart contract security is a high-risk field; always perform due diligence and consult with multiple professional auditors before deploying code to a mainnet environment.








![EVE Frontier Free Trial Access Runs From April 1 To 13 - ai smart contract [PR] EVE Frontier Free Trial Access Runs From April 1 To 13](https://www.geekmetaverse.com/wp-content/uploads/2026/03/eve-1-360x180.webp)